|
|
MX-M364N MX-565N (serv.man4)
Service Manual (Revised January 2016).
Service Manual
|
127
|
88.65 MB
|
|
|
MX-M364N MX-565N (serv.man5)
Installation Manual (Revised January2016).
Service Manual
|
127
|
45.47 MB
|
|
|
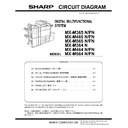
MX-M364N MX-565N (serv.man6)
Circuit Diagram
Service Manual
|
127
|
17.12 MB
|
|
|
MX-M364N MX-565N (serv.man7)
Parts Guide (Revised February 2017).
Service Manual / Parts Guide
|
127
|
22.26 MB
|
|
|
MX-M364N MX-565N (serv.man8)
PWB Parts Guide (Revised January 2016).
Service Manual / Parts Guide
|
74
|
1.1 MB
|
|
|
MX-M364N MX-565N (serv.man2)
CHANGE OF SENSOR AND SENSOR HOLDER
Service Manual / Specification
|
2
|
372.52 KB
|
|
|
MX-M364N MX-565N (serv.man3)
Specifications
Service Manual / Specification
|
7
|
148.44 KB
|
|
|
MX-M364N MX-565N (serv.man27)
CCE-1829 MODIFICATION OF PARTS DESIGN
Service Manual / Technical Bulletin
|
2
|
305 KB
|
|
|
MX-M364N MX-565N (serv.man28)
Firmware Update 8 - PCU 03.00.U1
Service Manual / Technical Bulletin
|
1
|
146.9 KB
|
|
|
MX-M364N MX-565N (serv.man29)
Parts change for productivity improvement.
Service Manual / Technical Bulletin
|
3
|
184.15 KB
|
|
|
MX-M364N MX-565N (serv.man30)
CCE 1785 DISCONTINUATION OF SUPPLY OF LAMP BASE
Service Manual / Technical Bulletin
|
4
|
400.71 KB
|
|
|
MX-M364N MX-565N (serv.man31)
Change in DV unit
Service Manual / Technical Bulletin
|
3
|
395.37 KB
|
|
|
MX-M364N MX-565N (serv.man32)
ARE-1234 -DESIGN CHANGE OF TRANSFER ROLLER BEARING R
Service Manual / Technical Bulletin
|
2
|
264.35 KB
|
|
|
MX-M364N MX-565N (serv.man33)
Change in UI for MX-M365 - MX-M565
Service Manual / Technical Bulletin
|
3
|
286.52 KB
|

|
MX-M364N MX-565N (serv.man34)
CHANGE OF TOUCH PANEL
Service Manual / Technical Bulletin
|
|
273.06 KB
|
|
|
MX-M364N MX-565N (serv.man35)
CHANGE OF OPERATION PANEL UNIT
Service Manual / Technical Bulletin
|
2
|
143.44 KB
|
|
|
MX-M364N MX-565N (serv.man36)
Change in SD card
Service Manual / Technical Bulletin
|
1
|
173.28 KB
|
|
|
MX-M364N MX-565N (serv.man37)
COUNTERMEASURE FOR CONTAMINATION ON PAPER EDGE AND PROCESS CONTROL DENSITY SENSOR ADJUSTMENT TROUBLE (F2-78)
Service Manual / Technical Bulletin
|
3
|
735.84 KB
|
|
|
MX-M364N MX-565N (serv.man38)
Change of PPD5 interface harness.
Service Manual / Technical Bulletin
|
2
|
108.01 KB
|
|
|
MX-M364N MX-565N (serv.man39)
CHANGE OF SPF HINGE
Service Manual / Technical Bulletin
|
2
|
575.03 KB
|
|
|
MX-M364N MX-565N (serv.man40)
CCE 1645 CHANGE OF TRANSPORT FOLLOWER ROLLER
Service Manual / Technical Bulletin
|
2
|
179.18 KB
|
|
|
MX-M364N MX-565N (serv.man41)
Firmware update for MX-FN17
Service Manual / Technical Bulletin
|
1
|
481.57 KB
|
|
|
MX-M364N MX-565N (serv.man42)
Change in material for winder pulley on optical baseplate unit (Correction).
Service Manual / Technical Bulletin
|
8
|
964.61 KB
|
|
|
MX-M364N MX-565N (serv.man43)
Firmware Update V03.00
Service Manual / Technical Bulletin
|
1
|
478.01 KB
|
|
|
MX-M364N MX-565N (serv.man44)
COUNTERMEASURE FOR DOG-EAR OR CREASE OF PAPER
Service Manual / Technical Bulletin
|
2
|
864.68 KB
|
|
|
MX-M364N MX-565N (serv.man45)
COUNTERMEASURE FOR PAPER CONTAMINATED WITH DROPPED TONER
Service Manual / Technical Bulletin
|
3
|
574.52 KB
|
|
|
MX-M364N MX-565N (serv.man46)
ADDITION OF FUSING WEB BRAKE SPRING
Service Manual / Technical Bulletin
|
2
|
615.47 KB
|
|
|
MX-M364N MX-565N (serv.man47)
Notification of CPO (License Manager) and support for SHA-2.
Service Manual / Technical Bulletin
|
3
|
38.6 KB
|
|
|
MX-M364N MX-565N (serv.man48)
CCE 1549 COUNTERMEASURE FOR NOISE FROM RSPF
Service Manual / Technical Bulletin
|
2
|
235.86 KB
|
|
|
MX-M364N MX-565N (serv.man49)
CCE 1508 IMPROVEMENT OF PERFORMANCE WHEN OPENING CLOSING DSPF LOWER DOOR
Service Manual / Technical Bulletin
|
3
|
235.02 KB
|
|
|
MX-M364N MX-565N (serv.man50)
Design change of delivery paper guide.
Service Manual / Technical Bulletin
|
2
|
91.45 KB
|
|
|
MX-M364N MX-565N (serv.man51)
CCE 1557 CHANGE OF SILENCE MOQUETTE ON RSPF
Service Manual / Technical Bulletin
|
2
|
203.99 KB
|
|
|
MX-M364N MX-565N (serv.man52)
Change of material in winder pulley on optical base plate unit.
Service Manual / Technical Bulletin
|
8
|
955.17 KB
|
|
|
MX-M364N MX-565N (serv.man53)
Change in shape of tension plate R for DSPF RSPF.
Service Manual / Technical Bulletin
|
3
|
217.95 KB
|
|
|
MX-M364N MX-565N (serv.man54)
Change in Fuser Frame
Service Manual / Technical Bulletin
|
2
|
357.94 KB
|
|
|
MX-M364N MX-565N (serv.man55)
Starting Powder List (This list takes priority over information in Service Manuals).
Service Manual / Technical Bulletin
|
4
|
66.25 KB
|
|
|
MX-M364N MX-565N (serv.man56)
CAUTION ILLUSTRATIONS ADDED TO PACKING BOX.
Service Manual / Technical Bulletin
|
1
|
83.72 KB
|
|
|
MX-M364N MX-565N (serv.man57)
CHANGE IN COLOR OF MC CLEANER SHAFT
Service Manual / Technical Bulletin
|
2
|
575.28 KB
|
|
|
MX-M364N MX-565N (serv.man58)
Rom Upgrade MX-FR45U
Service Manual / Technical Bulletin
|
2
|
508.76 KB
|
|
|
MX-M364N MX-565N (serv.man59)
ROM UPGRADE... (5) for MX-M364N - MX-M564N
Service Manual / Technical Bulletin
|
3
|
363.02 KB
|
|
|
MX-M364N MX-565N (serv.man60)
COUNTERMEASURE FOR PAPER CONTAMINATED WITH DROPPED TONER
Service Manual / Technical Bulletin
|
2
|
443.15 KB
|
|
|
MX-M364N MX-565N (serv.man61)
CCE 1466 RSPF ORIGINAL DETECT ACTUATOR STRENGTH IMPROVEMENT
Service Manual / Technical Bulletin
|
2
|
219.74 KB
|
|
|
MX-M364N MX-565N (serv.man62)
Material change Rotation Plate Sheet.
Service Manual / Technical Bulletin
|
3
|
290.1 KB
|
|
|
MX-M364N MX-565N (serv.man63)
MX-FR44U - ROM UPGRADE (4)
Service Manual / Technical Bulletin
|
3
|
366.47 KB
|
|
|
MX-M364N MX-565N (serv.man64)
CCE 1446 COUNTERMEASURE FOR NOISE FROM RIGHT LOWER DOOR UNIT, RIGHT DOOR UNIT AND MF PAPER FEED UNIT
Service Manual / Technical Bulletin
|
6
|
549.83 KB
|
|
|
MX-M364N MX-565N (serv.man65)
ROM UPGRADE... (6)
Service Manual / Technical Bulletin
|
3
|
370.44 KB
|
|
|
MX-M364N MX-565N (serv.man66)
COUNTERMEASURE FOR DOG-EAR OR CREASE OF PAPER
Service Manual / Technical Bulletin
|
3
|
528.99 KB
|
|
|
MX-M364N MX-565N (serv.man67)
CCE 1389R COUNTERMEASURE FOR E7-11 TROUBLE
Service Manual / Technical Bulletin
|
3
|
278.04 KB
|
|
|
MX-M364N MX-565N (serv.man68)
CCE 1439 NEWLY-REGISTERED SERVICE PARTS TO MODIFY PAPER JAM AND PAPER ALIGNMENT PROBLEM OCCURRED WHILE DISCHARGING PAPERS TO CENTER TRAY
Service Manual / Technical Bulletin
|
4
|
401.57 KB
|
|
|
MX-M364N MX-565N (serv.man69)
IMPROVEMENT FOR LOOSENESS OF M4 PLATE
Service Manual / Technical Bulletin
|
2
|
574.71 KB
|
|
|
MX-M364N MX-565N (serv.man70)
CHANGE OF BEARING FOR TONER HOPPER DRIVE SECTION OF MAIN DRIVE UNIT
Service Manual / Technical Bulletin
|
2
|
393.71 KB
|
|
|
MX-M364N MX-565N (serv.man71)
COUNTERMEASURE FOR UNAVAILABILITY OF HOME KEY INPUT
Service Manual / Technical Bulletin
|
2
|
445.5 KB
|
|
|
MX-M364N MX-565N (serv.man72)
Recommended shutdown procedure and Power Cycling of MFD
Service Manual / Technical Bulletin
|
1
|
186.43 KB
|
|
|
MX-M364N MX-565N (serv.man73)
IMPORTANT Handling of EEPROM's.
Service Manual / Technical Bulletin
|
5
|
203.32 KB
|
|
|
MX-M364N MX-565N (serv.man74)
DECREASING TORQUE LOAD ON HEAT ROLLER BY CHANGING THE SHAPE OF HR FIXING STOPPER
Service Manual / Technical Bulletin
|
2
|
445.62 KB
|
|
|
MX-M364N MX-565N (serv.man75)
ROM UPGRADE... (3)-(4)
Service Manual / Technical Bulletin
|
2
|
367.79 KB
|
|
|
MX-M364N MX-565N (serv.man76)
REMEDY FOR LOCKED PADDLE ROLLER, BROKEN PAWL ON MX GEAR R, AND BURNED MG ROLLER
Service Manual / Technical Bulletin
|
5
|
667.01 KB
|
|
|
MX-M364N MX-565N (serv.man77)
Prevention for mixing of foreign material into the clearance between PS front roller and PS roller earth plate and also false C4 error codes
Service Manual / Technical Bulletin
|
3
|
593.21 KB
|
|
|
MX-M364N MX-565N (serv.man78)
ROM Upgrade (5) For MX-M365N M465N M565N
Service Manual / Technical Bulletin
|
1
|
351.44 KB
|
|
|
MX-M364N MX-565N (serv.man79)
ROM Upgrade (2) For MX-FR45U (Option for MX-M364N M464N M564N)
Service Manual / Technical Bulletin
|
2
|
359.72 KB
|
|
|
MX-M364N MX-565N (serv.man80)
CCE 1410 FULL DETECT ERROR DUE TO FULL DETECT LEVER COMING OFF
Service Manual / Technical Bulletin
|
2
|
267.47 KB
|
|
|
MX-M364N MX-565N (serv.man81)
CCE 1409 REMEDY FOR NOISE FROM READING FRONT REAR ROLLER AND PS CLUTCH
Service Manual / Technical Bulletin
|
3
|
282.54 KB
|
|
|
MX-M364N MX-565N (serv.man82)
Improvement for noise and inconsistencies in pitch due to abrasion of fusing drive gear
Service Manual / Technical Bulletin
|
2
|
431.75 KB
|
|
|
MX-M364N MX-565N (serv.man83)
Change in material of pick up roller.
Service Manual / Technical Bulletin
|
2
|
77.2 KB
|
|
|
MX-M364N MX-565N (serv.man84)
CCE 1373 CHANGE OF WIRE LENGTH OF PAPER FEED HARNESS
Service Manual / Technical Bulletin
|
3
|
311.65 KB
|
|
|
MX-M364N MX-565N (serv.man85)
Change to upper HR bearing
Service Manual / Technical Bulletin
|
2
|
296.7 KB
|
|
|
MX-M364N MX-565N (serv.man86)
Change of 7 LCD LVDS PWB.
Service Manual / Technical Bulletin
|
2
|
293.2 KB
|
|
|
MX-M364N MX-565N (serv.man87)
Countermeasure for E7-11 trouble.
Service Manual / Technical Bulletin
|
3
|
125.27 KB
|
|
|
MX-M364N MX-565N (serv.man88)
Noise generated by right delivery belt
Service Manual / Technical Bulletin
|
3
|
433.77 KB
|
|
|
MX-M364N MX-565N (serv.man89)
Enhanced strength of gear 25 52T
Service Manual / Technical Bulletin
|
2
|
350.62 KB
|
|
|
MX-M364N MX-565N (serv.man90)
Parts change to MF upper guide section
Service Manual / Technical Bulletin
|
2
|
306.08 KB
|
|
|
MX-M364N MX-565N (serv.man91)
CCE 1386 CHANGE OF ASIC IN PCU PWB
Service Manual / Technical Bulletin
|
3
|
251.42 KB
|
|
|
MX-M364N MX-565N (serv.man92)
CCE 1383 REMEDY FOR NOISE FROM PS CLUTCH IN RSPF
Service Manual / Technical Bulletin
|
3
|
228.13 KB
|
|
|
MX-M364N MX-565N (serv.man93)
CCE 1372 COUNTERMEASURE FOR RECOGNITION FAILURE OF PCL PROGRAM FLASH ROM
Service Manual / Technical Bulletin
|
2
|
222.38 KB
|
|
|
MX-M364N MX-565N (serv.man94)
MATERIAL CHANGE WIDTH DETECT SENSOR FIXING PLATE.
Service Manual / Technical Bulletin
|
3
|
229.42 KB
|
|
|
MX-M364N MX-565N (serv.man95)
Modification of a clutch in the main drive unit
Service Manual / Technical Bulletin
|
2
|
267.62 KB
|
|
|
MX-M364N MX-565N (serv.man96)
Countermeasures against noise from transport follower roller.
Service Manual / Technical Bulletin
|
5
|
1.13 MB
|
|
|
MX-M364N MX-565N (serv.man97)
ROM Upgrade 4 for MX-M365N M465N M565N
Service Manual / Technical Bulletin
|
2
|
231 KB
|
|
|
MX-M364N MX-565N (serv.man98)
Remedy for noise generated while PS motor is rotating
Service Manual / Technical Bulletin
|
2
|
257.07 KB
|
|
|
MX-M364N MX-565N (serv.man99)
Part replacement to reduce paper jams at the fuser front side.
Service Manual / Technical Bulletin
|
2
|
304.85 KB
|
|
|
MX-M364N MX-565N (serv.man100)
CCE 1333R IMPROVEMENT OF NOISE FROM PAPER FEED REVERSE ROLLER
Service Manual / Technical Bulletin
|
2
|
194.71 KB
|
|
|
MX-M364N MX-565N (serv.man101)
CHANGE OF HDD MANUFACTURER.
Service Manual / Technical Bulletin
|
2
|
152.37 KB
|
|
|
MX-M364N MX-565N (serv.man102)
Enhancement of the durability of the upper HR thermistor
Service Manual / Technical Bulletin
|
2
|
290.19 KB
|
|
|
MX-M364N MX-565N (serv.man103)
Shape change to the MF pick sheet
Service Manual / Technical Bulletin
|
2
|
324.96 KB
|
|
|
MX-M364N MX-565N (serv.man104)
Improvement of noise from paper feed reverse roller
Service Manual / Technical Bulletin
|
2
|
316.2 KB
|
|
|
MX-M364N MX-565N (serv.man105)
Measures to prevent incorrect insertion of process unit
Service Manual / Technical Bulletin
|
2
|
293.22 KB
|
|
|
MX-M364N MX-565N (serv.man106)
Countermeasure to prevent DV belt B from falling off resulting in toner dispersion and blank pages etc.
Service Manual / Technical Bulletin
|
5
|
628.63 KB
|
|
|
MX-M364N MX-565N (serv.man107)
Countermeasure for noise from transport follower roller
Service Manual / Technical Bulletin
|
5
|
950 KB
|
|
|
MX-M364N MX-565N (serv.man108)
Improved MC cleaning performance
Service Manual / Technical Bulletin
|
2
|
322.77 KB
|
|
|
MX-M364N MX-565N (serv.man109)
CCE 1332 COUNTERMEASURE FOR NOISE FROM TRANSPORT FOLLOWER ROLLER
Service Manual / Technical Bulletin
|
5
|
819.33 KB
|
|
|
MX-M364N MX-565N (serv.man110)
Countermeasure for breakage of spring pin in fusing rear joint shaft unit
Service Manual / Technical Bulletin
|
2
|
317.56 KB
|
|
|
MX-M364N MX-565N (serv.man111)
ROM Upgrade (2) - MX-FR44U (Option for MX-M365N M465N M565N)
Service Manual / Technical Bulletin
|
1
|
199.56 KB
|
|
|
MX-M364N MX-565N (serv.man112)
MX-M365N M465N M565N - ROM Upgrade ICU V0201o1 - PCU V0300o1
Service Manual / Technical Bulletin
|
1
|
212.94 KB
|
|
|
MX-M364N MX-565N (serv.man114)
CCE-1321 ENHANCEMENT OF MF ROTATION PAWL SPRING
Service Manual / Technical Bulletin
|
2
|
127.18 KB
|
|
|
MX-M364N MX-565N (serv.man115)
ROM Upgrade - MX-FR45U (Option for MX-M364N M464N M564N)
Service Manual / Technical Bulletin
|
1
|
210.53 KB
|
|
|
MX-M364N MX-565N (serv.man116)
ROM Upgrade (1) - MX-FR44U (Option for MX-M365N M465N M565N)
Service Manual / Technical Bulletin
|
2
|
220 KB
|
|
|
MX-M364N MX-565N (serv.man117)
MX-M364N M464N M564N - ROM Upgrade ICU V0200u1 - PCU V0300o1
Service Manual / Technical Bulletin
|
2
|
213.46 KB
|
|
|
MX-M364N MX-565N (serv.man118)
MX-M365N M465N M565N - ROM Upgrade ICU V0200o1 - PCU V0300o1
Service Manual / Technical Bulletin
|
2
|
215.76 KB
|
|
|
MX-M364N MX-565N (serv.man119)
Procedure for using Service Personnel Oriented Functions in Sharp Remote Device Manager.
Service Manual / Technical Bulletin
|
18
|
2.11 MB
|
|
|
MX-M364N MX-565N (serv.man120)
Change in Colour of the Drum
Service Manual / Technical Bulletin
|
1
|
203.17 KB
|
|
|
MX-M364N MX-565N (serv.man121)
Setup of new service part - Paper Feed Drive Sub Unit
Service Manual / Technical Bulletin
|
2
|
258.03 KB
|
|
|
MX-M364N MX-565N (serv.man122)
CCE-1297 TOUCH PANEL ENTRY TROUBLE
Service Manual / Technical Bulletin
|
2
|
117.79 KB
|
|
|
MX-M364N MX-565N (serv.man123)
CCE-1282 IMPROVEMENT OF PAPER FEEDING RELIABILITY OF BYPASS TRAY BY CHANGING THE SHAPE OF MF CAM COLLAR
Service Manual / Technical Bulletin
|
2
|
233.14 KB
|
|
|
MX-M364N MX-565N (serv.man124)
MODIFICATION OF CONTROL PWB FOR PRODUCTIVITY IMPROVEMENT.
Service Manual / Technical Bulletin
|
1
|
26.79 KB
|
|
|
MX-M364N MX-565N (serv.man125)
COUNTERMEASURE FOR TONER CONTAMINATION ON CENTRE OF BACK SIDE OF PAPER.
Service Manual / Technical Bulletin
|
4
|
440.04 KB
|
|
|
MX-M364N MX-565N (serv.man126)
Firmware release to support finishing options
Service Manual / Technical Bulletin
|
1
|
198.17 KB
|
|
|
MX-M364N MX-565N (serv.man127)
For MX-DE13 DE14 - Firmware Upgrade and Change of transport motor
Service Manual / Technical Bulletin
|
2
|
345.8 KB
|
|
|
MX-M364N MX-565N (serv.man128)
Amendment of note when replacing the drum
Service Manual / Technical Bulletin
|
1
|
201.41 KB
|

|
MX-M364N MX-565N (serv.man9)
Orion IT firmware MXM365N, MXM465N, MXM565N V3
Driver / Update
|
|
211.61 MB
|

|
MX-M364N MX-565N (serv.man10)
PCU 03.00.U1
Driver / Update
|
|
49.51 MB
|

|
MX-M364N MX-565N (serv.man11)
Firmware Update for MX-M365 M465 M565.
Driver / Update
|
|
211.61 MB
|

|
MX-M364N MX-565N (serv.man12)
MX-FN17 Firmware Update for MX-M364 M464 M564 (ARE-1212)
Driver / Update
|
|
603.15 KB
|

|
MX-M364N MX-565N (serv.man13)
MX-FN17 Firmware Update for MX-M365 M465 M565 (ARE-1212)
Driver / Update
|
|
603.14 KB
|

|
MX-M364N MX-565N (serv.man14)
Firmware Update for MX-M364 M464 564 (ARE-1210)
Driver / Update
|
|
49.59 MB
|

|
MX-M364N MX-565N (serv.man15)
Special Firmware for PPD2_FIN Jams for MX-M365N 465N 565N
Driver / Update
|
|
303.25 KB
|

|
MX-M364N MX-565N (serv.man16)
Special Firmware for PPD2_FIN Jams for MX-M364N 464N 564N
Driver / Update
|
|
303.25 KB
|

|
MX-M364N MX-565N (serv.man17)
MX-FR45U
Driver / Update
|
|
49.85 MB
|

|
MX-M364N MX-565N (serv.man18)
ROM UPGRADE... (5) for MX-M364N - MX-M564N inc bulletin
Driver / Update
|
|
49.71 MB
|

|
MX-M364N MX-565N (serv.man19)
MX-FR44U DSK Firmware Update (4)
Driver / Update
|
|
211.35 MB
|

|
MX-M364N MX-565N (serv.man20)
ROM UPGRADE..(6) For MX-M365N M465N M565N - Tech Bulletin Inc
Driver / Update
|
|
211.63 MB
|

|
MX-M364N MX-565N (serv.man21)
CCE-1317 MX-FR44 MXM365-565 OPEN SSL VULNERABILITY DSK ONLY FIRMWARE RELEASE FOR FIELD SUPPORT VERSION
Driver / Update
|
|
208.3 MB
|

|
MX-M364N MX-565N (serv.man22)
MX-FR45U (Option for MX-M364N M464N M564N)
Driver / Update
|
|
49.47 MB
|

|
MX-M364N MX-565N (serv.man23)
MX-M365 M465 M565 FIRMWARE 02.00 Firmware to fix potential vulnerability of OpenSSL
Driver / Update
|
|
210.29 MB
|

|
MX-M364N MX-565N (serv.man24)
Production Firmware for MX-M365 M465 M565
Driver / Update
|
|
215.22 MB
|

|
MX-M364N MX-565N (serv.man25)
Watermark Firmware
Driver / Update
|
|
6.32 MB
|

|
MX-M364N MX-565N (serv.man26)
Production Firmware for MX-M364 M464 M564
Driver / Update
|
|
49.08 MB
|
|
|
MX-M364N MX-565N
NOTE - Handy Guides are NOT a substitute for Service Manuals and Parts Guides
Handy Guide
|
60
|
2.5 MB
|
|
|
MX-M364N MX-565N (serv.man129)
MSDS for MX-560GV.
Regulatory Data
|
9
|
121.48 KB
|
|
|
MX-M364N MX-565N (serv.man130)
MSDS for MX-560GT.
Regulatory Data
|
9
|
119.51 KB
|